Move over, fake admirers—there’s a new dating app scam in town, and it’s not here to break your heart, but to steal your data. If you’re an Android user who’s ever searched for romance online, stay sharp: cybercriminals have launched a massive spyware campaign cloaked as an innocent dating app, and the only match you’ll make is with trouble.
A trojan horse in your search for love
A rogue dating app is currently on the hunt for unsuspecting Android users. Researchers at ESET have uncovered that this fake app is acting as a Trojan horse for the GhostChat virus, a piece of malware ready to pillage all your personal data. Meanwhile, a hacker chatting with you on WhatsApp poses as a potential lover—all part of a vast espionage campaign that targets both smartphones and computers alike.
How the fake dating app hooks its victims
This wide-reaching spy operation specifically targets Android smartphones. The malicious app poses as a legitimate online dating platform and even claims direct integration with WhatsApp—a detail no doubt designed to add credibility and lure in hopeful singles. The app is being circulated widely on the internet as downloadable APK files, a classic move for threats lurking outside the official Google Play Store.
To reel in its targets, the scammers copied the icon of a real dating app available on the Play Store called Dating Apps without payment. But don’t be fooled: the sole purpose of the fraudulent app is to secretly install the malware GhostChat onto victims’ devices.
Once installed, the app displays an array of seemingly “locked” female profiles. According to ESET's findings, the home page features 14 fake female profiles—a crafty trick to spark curiosity and encourage users to try unlocking these alluring contacts.
Social engineering with a sprinkle of ‘Exclusive' access
Before chatting with any of these fake profiles, the user is prompted to enter an access code, which they conveniently receive straight away. This little hoop to jump through gives the user the impression of using a premium, members-only service. But in reality, it’s just a case of smoke and mirrors. The researcher behind this discovery, Lukas Stefanko, explains:
“It’s simply a social engineering technique likely designed to create the illusion of ‘exclusive access’ for potential victims.”
Once a victim enters the code and “unlocks” a profile, they’re funneled into a WhatsApp conversation with one of these bogus accounts. While the person believes they’re chatting with a genuine love interest, they’re actually communicating with cybercriminals—or, just as charming, a dedicated bot.
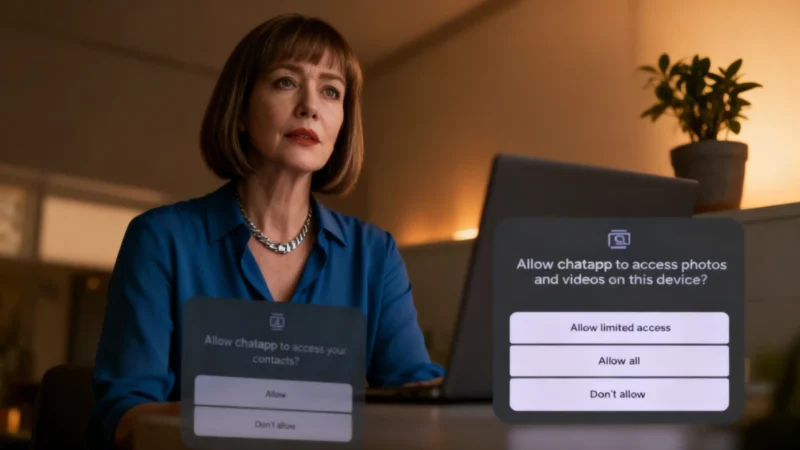
Meanwhile, GhostChat quietly gets to work in the background, scanning all files on the device, harvesting photos taken with the phone, scraping the complete contact list, and regularly shipping everything off to a remote server. Every new photo added to the camera roll is automatically transferred to the hackers—piles of personal data changing hands in no time.
By continuing the WhatsApp chat, the hackers ensure the malware sticks around long enough to hoover up as much data as possible. The ongoing conversation reassures the victim that the dating platform is legit, when in fact, it's a scam. The researcher summarizes it succinctly as:
“A new kind of romance scam technique.”
A whole arsenal of threats: Beyond dating apps
ESET researchers warn that GhostChat is only the tip of the iceberg in a broader espionage campaign. The same criminal group has ramped up attacks against Windows computers, delivering ClickFix-style operations. In these, victims are tricked into running malicious code themselves by following illicit instructions. Relying on bogus government-lookalike websites and displaying fake security alerts, these ClickFix attacks have recently surged, targeting not just Windows, but also Facebook and Google Chrome users.
The group hasn’t stopped there. They’re also orchestrating attacks based on a mechanism called GhostPairing. This sneaky tactic abuses WhatsApp’s “Linked Devices” feature to spy on or even fully take over a user's account—no need to swipe their password or login details. Again, the operation leans on a fake government portal: the site invites users to join an “official” WhatsApp group, and—here’s the kicker—to enter, victims must scan a QR code with their phone.
Surprise! That QR code doesn’t take you to the group. Instead, it silently links the victim’s WhatsApp account to a device controlled by the hackers using WhatsApp's “Linked Devices” feature. Once “GhostPairing” is in place, attackers can sift through chat histories, contact lists, and every future message sent or received, as though they’re sitting right there inside the target’s account.
At present, these attacks are specifically aimed at people residing in Pakistan. As always, the golden rule applies: don’t install unknown apps outside the Play Store, no matter how convincing (or how promising their dating profiles might be).